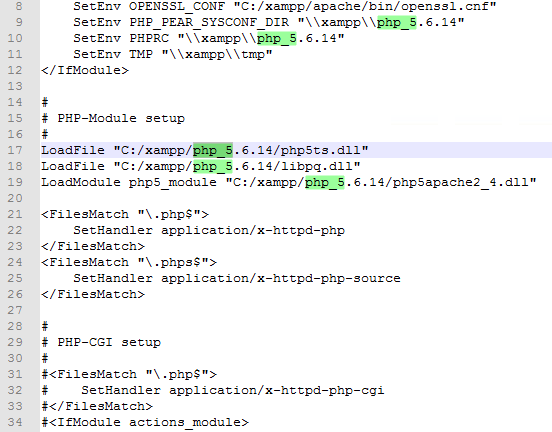
I needed to upgrade the bundled php-version 6.5.12 to the latest 6.5.14 due to some security vulnerabilities. This is how I upgraded php in XAMPP to the latest version.
– Multiple use-after-free memory errors exist related to the unserialize() function, which a remote attacker can exploit to execute arbitrary code. (CVE-2015-6834)
– A use-after-free memory error exists related to the php_var_unserialize() function. A remote attacker, using a crafted serialize string, can exploit this to execute arbitrary code. (CVE-2015-6835)
– A type confusion error exists related to the serialize_function_call() function due to improper validation of the headers field, which a remote attacker can exploit to have unspecified impact. (CVE-2015-6836)
– An flaw exists in the XSLTProcessor class due to improper validation of input from the libxslt library, which a remote attacker can exploit to have an unspecified impact. (CVE-2015-6837, CVE-2015-6838)
– A flaw exists in the php_zip_extract_file() function in file php_zip.c due to improper sanitization of user-supplied input. An unauthenticated, remote attacker can exploit this to create arbitrary directories outside of the restricted path. (OSVDB 127122)
– A NULL pointer dereference flaw exists in the spl_autoload() function in file php_spl.c due to improper sanitization of user-supplied input. An unauthenticated, remote attacker can exploit this to cause a PHP application to crash. (OSVDB 127124)
– A flaw exists in the parse_ini_file() and parse_ini_string() functions due to improper sanitization of user-supplied input. An unauthenticated, remote attacker can exploit this to cause a PHP application to crash. (OSVDB 127125)
– A flaw exists in the CLI SAPI Web Server due to improper sanitization of user-supplied input. An unauthenticated, remote attacker can exploit this to access arbitrary files outside of the restricted path. (OSVDB 127126)
RRS feed